Exposing the Insecurity: How SS7 Flaws Threaten Our Modern Communication Systems
Awareness and proactive measures are essential to protect against the vulnerabilities of outdated SS7 networks as we transition to more secure communication systems
I was inspired to write this article after watching a video on the Veritasium channel titled “I Hacked My Friend's Phone to Show How Easy It Is.” I highly recommend everyone watch it, as it demonstrates how alarmingly simple it is to hack a phone connected to the SS7 network. While the video does a great job of explaining the system and its vulnerabilities, it may be challenging for someone without a technical background to grasp the full extent of how this hacking works and how the transition to 5G enhances security against such threats. The video illustrates how easily unauthorized access to the SS7 network can be obtained—a network used by all 2G and 3G systems—and how rogue state actors can exploit these vulnerabilities to spy on their citizens and even on people in other countries. In this article, I will break down these issues in a way that is accessible to everyone and explore why some individuals have resorted to using pagers to avoid surveillance, which led to a controversial incident in Lebanon recently when several pagers were simultaneously compromised. This will be an engaging discussion, and I promise you will find it both informative and intriguing. By the end, I’ll also share practical tips on how to protect yourself and secure your financial transactions from such attacks.
Why do we need SS7 signaling?
SS7 (Signaling System 7) was developed to facilitate the routing of calls between phones, whether fixed or mobile, ensuring that each call reaches its intended destination. Think of it like the postal system: when you send a letter, you include both your address and the recipient’s address, and the postal system acts as an intermediary, routing the letter through various sorting centers until it arrives at its destination. Similarly, when you make a phone call, the SS7 signaling system acts as an automated routing mechanism, dynamically managing the connection between the calling and receiving parties without the need for human intervention. It’s like a digital postman, ensuring that your call is delivered accurately and efficiently.
Why is SS7 Signaling Vulnerable?
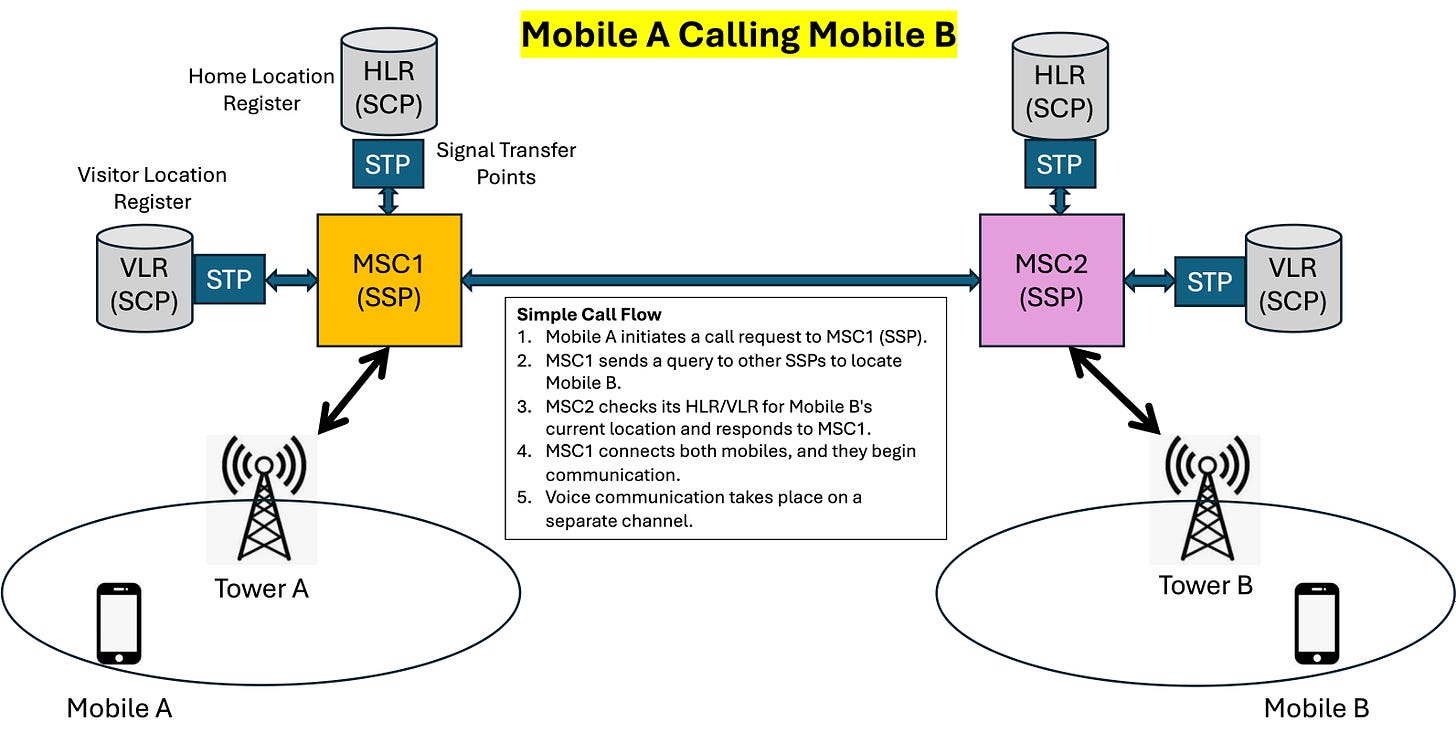
In mobile networks, SS7 is more vulnerable to attacks compared to fixed-line networks, which have dedicated connections to specific switches. A typical mobile network consists of various signaling points, including SSPs (Service Switching Points), STPs (Signal Transfer Points), and SCPs (Service Control Points). The SSP is a network element within the operator’s infrastructure that controls call setup, routing, and termination. It is not the mobile phone itself, but the point in the network to which your phone connects. STPs act as traffic controllers, routing signaling messages between SSPs, while SCPs handle additional services such as number portability and balance checks.
When you dial a number, your phone connects to the network's SSP, which sends a signaling message through an STP to the destination SSP. The destination SSP sends a response back, confirming the caller’s phone is ringing. Once the call is answered, a separate voice path is established for the conversation. If the call fails, the SS7 network returns an error message explaining why.
The following diagram explains the simple call flow.
The vulnerability arises because these network elements trust each other implicitly and do not verify the authenticity of signaling messages, and also these messages are transmitted in clear text form without any encryption.
This means that if an attacker gains access to the SS7 network—typically through a compromised or rogue network element—they can masquerade as a legitimate node. This allows them to intercept calls and messages, track user locations, or reroute traffic, all without detection. Note - Regular mobile users do not have this capability; such attacks require direct access to the SS7 network infrastructure.
How is the SS7 Signaling System Hacked?
It’s surprisingly simple. All a hacker needs is access to the SS7 network, which can be obtained through a rogue telecom operator or a compromised network element, often under the influence of state-controlled agencies. Once inside the system, the hacker only needs the target’s mobile number. With this, the attacker masquerades as a legitimate MSC (Mobile Switching Center) and sends a query known as a "Send Routing Info for SM" (SRI-SM) or a "Provide Subscriber Info" (PSI) message to the Home Location Register (HLR). The HLR, which keeps track of the subscriber’s location, will respond with the current Visitor Location Register (VLR) where the target is registered, whether at home or roaming.
Next, the attacker sends an "Update Location" message to the HLR, pretending that the target has moved to the attacker’s VLR or MSC. This tricks the HLR into believing that the user has changed locations. Once the HLR updates its records with the attacker’s fake VLR, all incoming calls and messages meant for the target are rerouted to the attacker’s VLR or MSC. This allows the attacker to intercept and manipulate the target’s communications, often without the target or legitimate network elements being aware.
How are Mobile Locations Tracked in an SS7 System?
An SS7 system tracks the location of mobile phones without the need for GPS. The process is straightforward: any mobile device connected to the network must regularly report its location to the network by registering with the nearest cell tower (BTS). This information is stored in the Visitor Location Register (VLR), which keeps track of the mobile’s location at the granularity of the cell tower level. This allows the network to know the approximate location of the device in real time.
Once the mobile’s location is recorded in the VLR, any SS7 element with access to the network can potentially retrieve this information, unless the network is properly secured with SS7 firewalls. These firewalls must be sophisticated enough to detect whether incoming requests for location information are legitimate or malicious. They do this by analyzing the source of the request, such as flagging suspicious queries from countries where SS7 access can be obtained easily, sometimes through bribery. However, filtering becomes increasingly challenging when state actors are involved, as they can bypass these security measures.
Due to these vulnerabilities, some organizations have reverted to using pager systems, which operate outside the SS7 infrastructure. This makes it more difficult for attackers to track individuals by impersonating a legitimate SS7 node.
Why is a 5G/4G IMS-Based System More Secure Than a 2G/3G SS7 System?
An IMS (IP Multimedia Subsystem) SIP-based signaling system used in 4G and 5G networks is more secure than the SS7 signaling system used in 2G and 3G networks. This is because IMS uses encrypted end-to-end authentication, ensuring that the user’s identity is securely encrypted and embedded within the signaling messages. These messages can only be read by the intended recipient elements, making it nearly impossible for unauthorized entities to intercept or manipulate them. In contrast, SS7 messages are transmitted in plaintext, which makes them vulnerable to eavesdropping and manipulation by any rogue element with SS7 access.
In an IMS system, even if signaling messages are intercepted by a hacker or routed through compromised servers, they cannot be deciphered or altered without breaking the encryption, which is virtually impossible without malware or a security breach on the originating device.
This is why 4G and 5G networks using SIP protocols are much more secure and less susceptible to attacks compared to legacy SS7 systems.
However, the transition to SIP-based authentication is not straightforward. The telecom infrastructure still relies on SS7 for compatibility with older 2G and 3G networks. Many trunk exchanges, which connect different network systems, still use SS7 for interconnection with legacy networks. This means that even with 4G and 5G networks in place, the overall system remains vulnerable, as the weakest link—SS7-based trunk exchanges—can be exploited.
This backward compatibility requirement makes even modern systems susceptible to attacks, especially by state-sponsored actors who can exploit these legacy vulnerabilities.
What Can We as Users Do to Protect Ourselves from Such Attacks?
There are several steps that both users and telecom operators can take to enhance security. As users, the first and most crucial step is to avoid using SMS for two-factor authentication (2FA), as it is vulnerable to SS7-based attacks. Instead, use more secure alternatives such as hardware tokens or authenticator apps (like Google Authenticator or Authy) for generating 2FA codes. Additionally, ensure that your passwords are strong and not susceptible to brute-force attacks.
While accessing the SS7 network is challenging in countries with strong legal and corporate safeguards, it can be relatively easy in countries with weak regulations and enforcement. This poses a risk, especially for SMS-based authentication in financial transactions. Therefore, avoid SMS-based 2FA for sensitive activities and use more secure methods instead.
Telecom operators also have a responsibility to protect their users. They should implement SS7 firewalls to block suspicious location requests and monitor for unusual activity. For secure communication, consider using encrypted messaging and calling apps like WhatsApp or Signal, which offer better protection against interception compared to regular SMS or voice calls.
Unfortunately, when it comes to location tracking, there’s little users can do if state agencies misuse their access to the SS7 network to obtain location data. Although not as precise as GPS, SS7 can still pinpoint a user’s location to the level of a cell tower. This has led some organizations to revert to using legacy pager systems, which operate on a completely different architecture, making them immune to such tracking.
Conclusion
The communication systems we rely on today are riddled with vulnerabilities, particularly in legacy SS7 networks that were designed long before the internet era. These systems operate on the outdated assumption that all network operators are trustworthy and responsible, which is far from reality. As SS7 networks have proliferated into regions with weak legal and ethical standards, the potential for abuse has escalated, especially with state actors exploiting these flaws to surveil their own citizens and monitor international targets.
The only true solution to these vulnerabilities is to completely phase out 2G and 3G systems that use SS7 signaling—a daunting task that is unlikely to be achieved anytime soon. Until then, both individuals and organizations need to be proactive in securing their communications. Avoid SMS-based two-factor authentication for financial transactions; instead, use secure methods like authenticator apps or hardware tokens. Keep your passwords robust and your devices free of malware, though even this can be challenging in the face of sophisticated, state-sponsored cyber operations.
Ultimately, the best defense is awareness. Understand the risks, push for SIP-based systems where possible, and support the decommissioning of legacy networks. While modern communication technology has brought immense convenience and connectivity, it has also opened the door to unprecedented levels of surveillance and cyber threats. Navigating this landscape requires vigilance, proactive measures, and an understanding that in the ever-evolving game of cybersecurity, staying one step ahead is our best bet.